Setup and administration for Transformations
You can use OpenID Connect and your existing identity provider (IdP) framework to manage access to CDF data securely. We currently support Microsoft Entra ID, Microsoft's cloud-based identity and access management service.
This article explains how a Microsoft Entra ID (ME-ID) administrator can control access to Transformations using the organization's IdP.
When you have registered Transformations, users can sign in with their organizational ID to transform data in a CDF project.
CDF projects running in Google Cloud Platform need to be allowlisted to support scheduling of transformations using OpenID Connect (OIDC) credentials. Contact your Cognite representative to be added to the allowlist.
Before you start
Make sure you have registered the Cognite API and the CDF application in Microsoft Entra ID and set up Microsoft Entra ID and CDF groups to control access to CDF data.
To perform the steps below, you need to be an administrator of Azure AD.
Step 1: Register an app in Microsoft Entra ID to use with Transformations
-
Sign in to the Azure portal as an admin.
-
If you have access to multiple tenants, use the Directory + subscription filter
 in the top menu to select the tenant in which you want to register an application.
in the top menu to select the tenant in which you want to register an application. -
Search for and select Microsoft Entra ID.
-
Under Manage, select App registrations > New registrations.
-
In the Register an application window, enter the app name, and then select Register.
-
Copy and make a note of the Application (client) ID. This value is required for authentication when reading and writing data in Transformations.
-
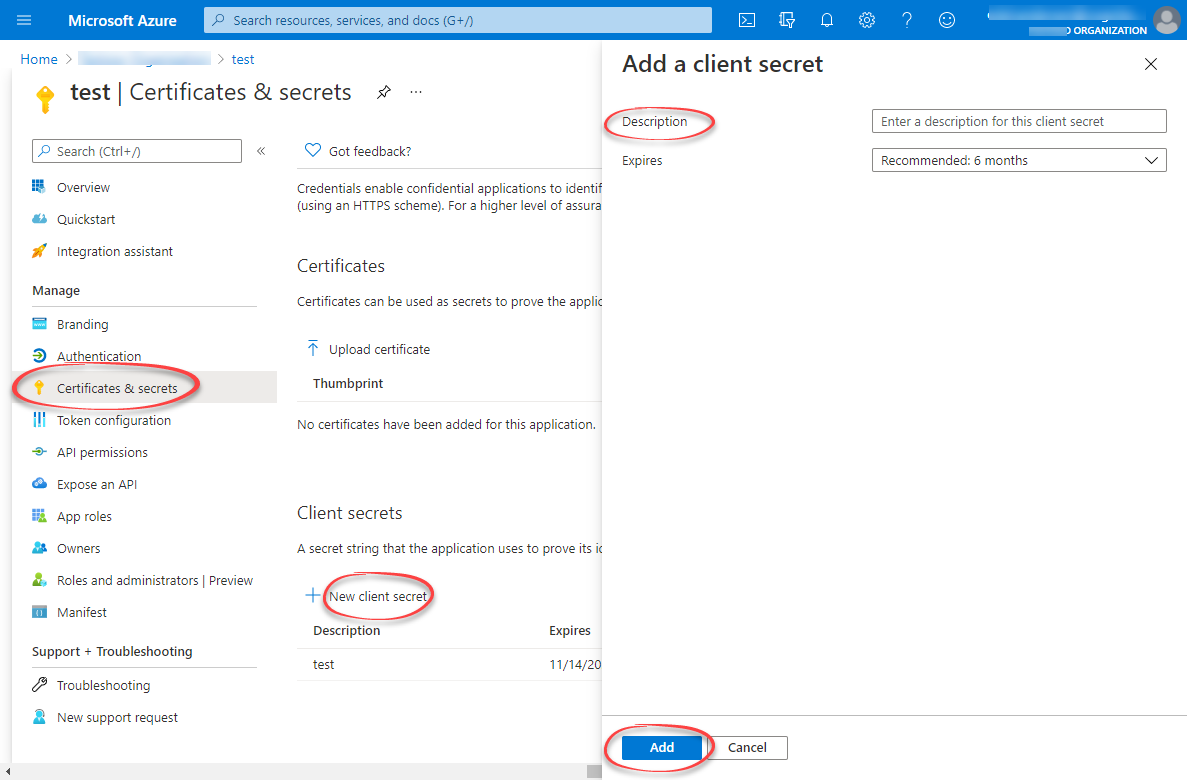
Under Manage, select Certificates & secrets > New client secret.
-
Enter a client secret description and an expiry time, and then select Add.
-
Copy and make a note of the client secret in the Value field.
importantMake sure you copy this value now. This value will be hidden after you leave this page.
Step 2: Create a group in Azure AD and add the registered app as its member
-
Open the overview window in Azure AD and select Manage > Groups.
-
Create a group.
-
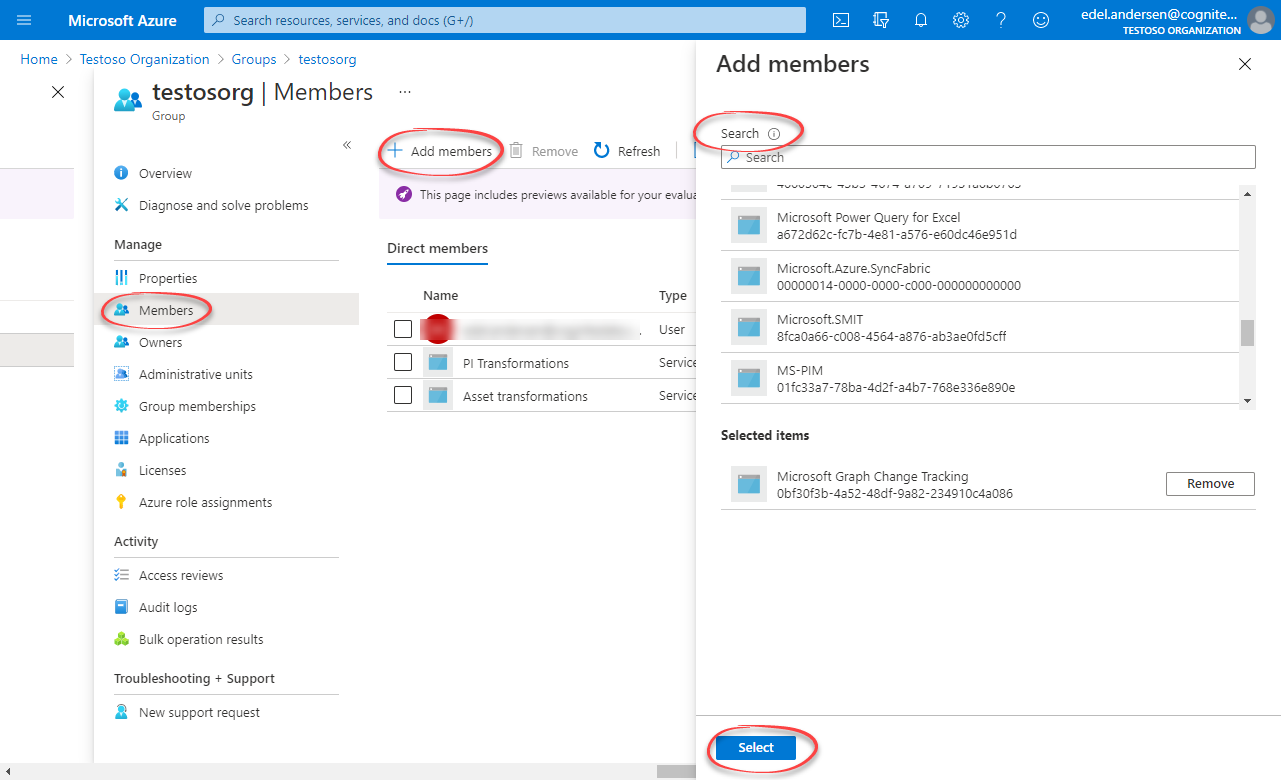
Open the group. Under Manage, select Members > Add members.
-
Find the app you created above and click Select.
-
Add all users you want to have access to Transformations as members.
-
Return to the overview, and then copy and make a note of the Object Id.
Step 3: Create a group in CDF and link to the Microsoft Entra ID group
-
Sign into CDF as an admin and navigate to Access > Groups.
-
Select Create new group and enter a unique name for the group.
-
Add
readandwritecapabilities accordingly for the CDF resources you want to read and write using transformations. For instance, if you are transforming the data in CDF RAW and writing the data to assets, you must addraw:readandasset:writecapabilities.Minimum required capabilitiesThe minimum requirement is to add
projects:list,groups:list,transformations:read,transformations:write, andsessions:create. -
Select Create.
-
Open the OpenID connect tab and insert your
token_url. Thetoken_urlcontains the ID of your Microsoft Entra ID tenant. To find your tenant ID, see this article.Running scheduled transformationsTo schedule transformations, you must add the capability
sessions:createand set thetoken_urlto maintain access to Transformations for an extended time period.To enable Run as current user for transformations, you must add the
sessions:createcapability. -
Link the transformations group to a Microsoft Entra ID group:
-
In the Source ID field, enter the Object Id for the AAD group exactly as it exists in AAD. You can use the same group Id for multiple transformations.
-
In the Source name field, enter the name of the group in Azure AD.
-
Step 4: Run transformations
-
Verify that the configuration is successful by following the steps in this article.
noteTransformations with the same Client ID run as the same user with the same access. This ID and the Client secret must be given before a user can schedule and run transformations.