You can use OpenID Connect and your existing identity provider (IdP) framework to manage access to CDF data securely. We currently support Microsoft Entra ID, Microsoft’s cloud-based identity and access management service. Follow the steps below to connect to a CDF project with OpenID Connect and use CDF as a data source in Grafana.Documentation Index
Fetch the complete documentation index at: https://docs.cognite.com/llms.txt
Use this file to discover all available pages before exploring further.
Before you start
Make sure that you have administrator access to your Grafana instance. We support the Enterprise, self-hosted and Cloud Pro editions of Grafana. We also support free cloud instances, but then you need to set up a client credentials grant flow for each instance of the Cognite Data Source.Step 1: Register Grafana as an application in Microsoft Entra ID
The Cognite Data Source for Grafana uses the credentials you use to sign in to Grafana to connect to CDF. Therefore, you need to set up the Grafana instance to authenticate the user towards the same identity provider (IdP) as your CDF project. The first step is to configure the Grafana instance to use OAuth2. The example below uses Microsoft Entra ID as the IdP.Register the Cognite API and CDF application
Enable Microsoft Entra ID authentication in Grafana
scopes = openid email profile offline_access https://<your-cluster>.cognitedata.com/user_impersonation https://<your-cluster>.cognitedata.com/IDENTITYRestart the Grafana service
Verify configuration as administrator
Step 2: Decide access to CDF data
Link Microsoft Entra ID and CDF groups
Configure required capabilities
-
timeSeriesAcl:READ:required to find and plot time series. -
groupsAcl:LIST:required to verify Grafana connectivity. -
projectsAcl:LIST:required to verify Grafana connectivity. -
assetsAcl:READ:optional to use template variables and select time series from an asset. -
eventsAcl:READ:optional to use annotations.
Step 3: Install the Cognite Data Source for Grafana
To install the Cognite Data Source for Grafana:- Grafana Enterprise
- Self-hosted Grafana
Install the plugin
Step 4: Configure the Cognite Data Source for Grafana
To configure the Cognite Data Source for Grafana:Add the Cognite data source
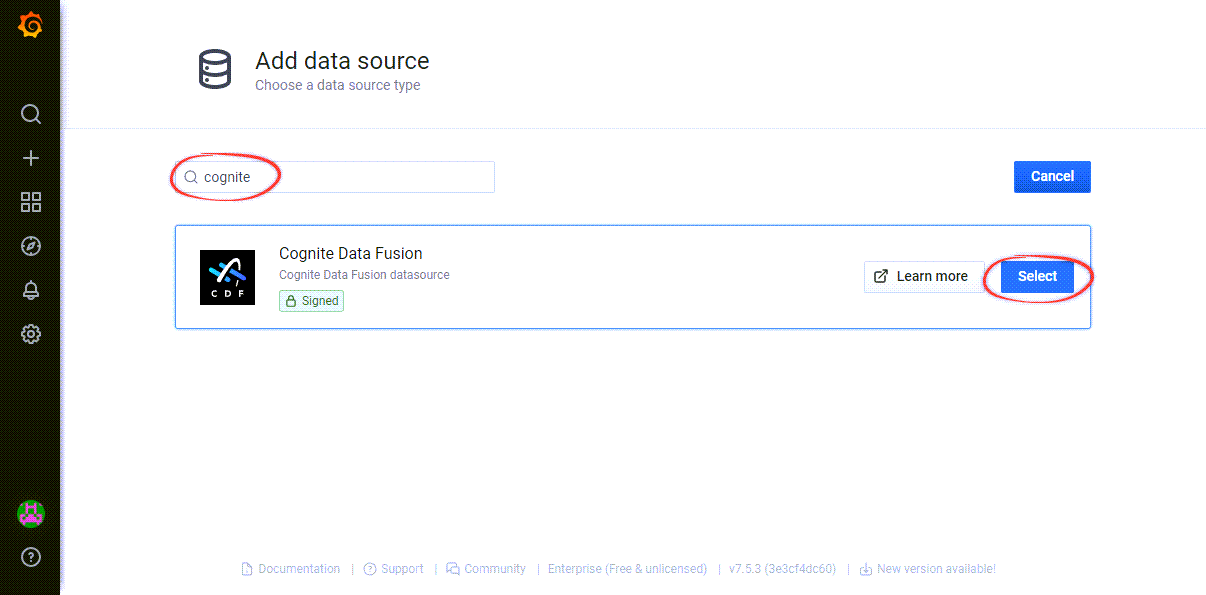
Configure the data source
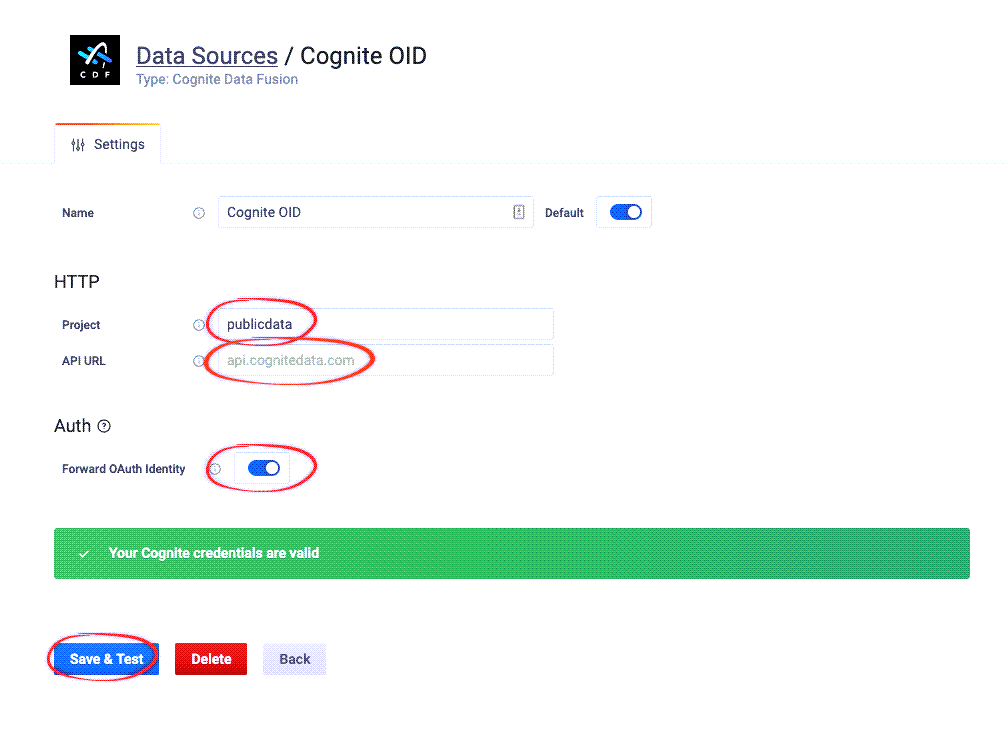
Verify the configuration
Set up a client credentials grant flow
In some cases, for example, if you’re using the Grafana free tier, you can not set up an identity provider for the whole Grafana instance. Instead, follow these steps to set up a client credentials grant flow for each instance of the Cognite Data Source:Before you start
Set up application registration
Register Cognite API and CDF application
Configure required capabilities
Add service principal to CDF group
Install the plugin
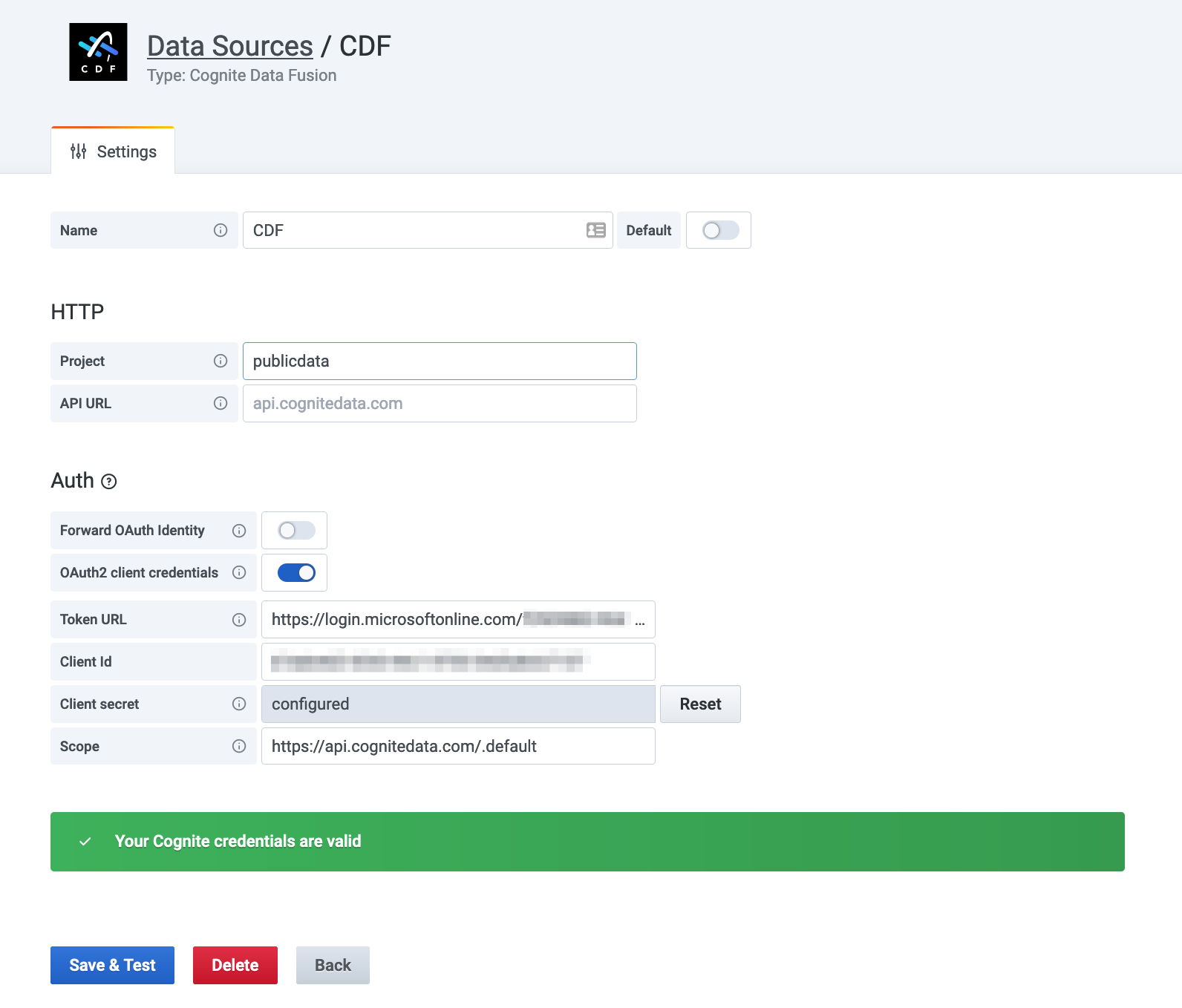
Configure OAuth2 client credentials
- Disable Forward OAuth identity.
- Enable OAuth2 client credentials.
- Enter the credentials.